SSL additions to ProxySQL v2.3.0!
Introducing ProxySQL dynamic SSL
Feature description
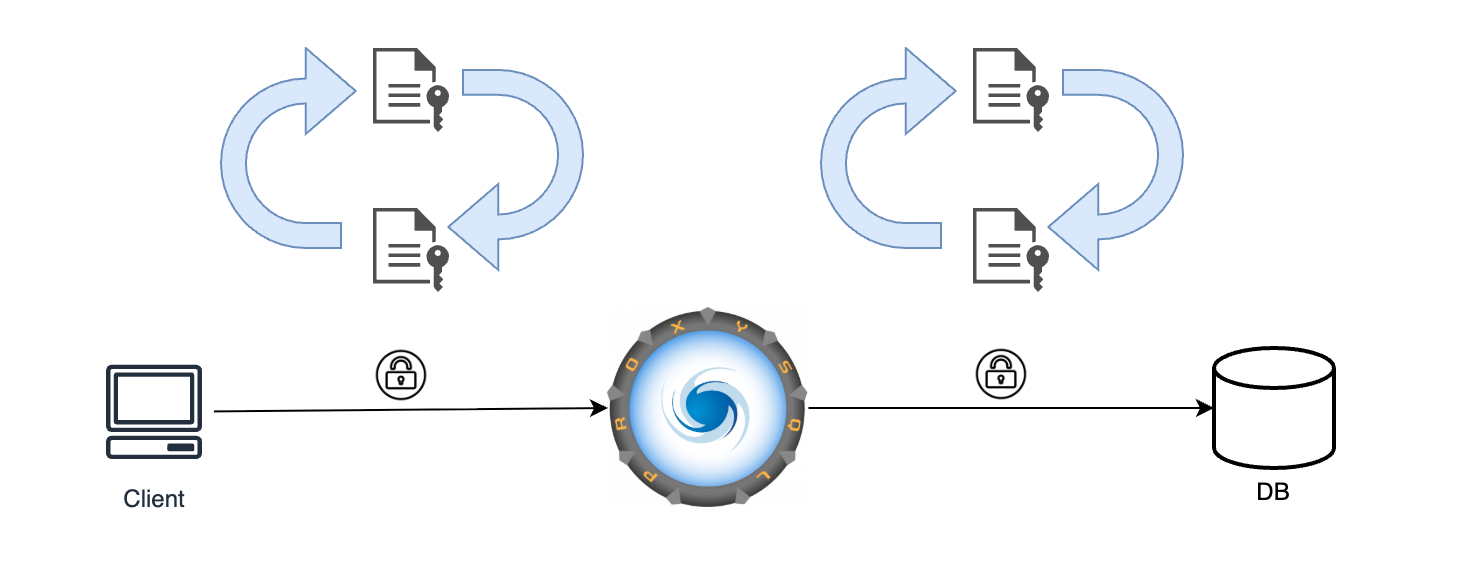
Since v2.3.0 the TLS context that ProxySQL uses for new connections is now reconfigurable at runtime. This capability allows the reloading of certificates used for client SSL contexts without requiring to restart ProxySQL. This, in combination with the already present capability of changing the certificates being used for backends connections, allows for a complete renewal of the SSL certificates used by ProxySQL with zero downtime.
An important consideration is remembering that the certificates will only be effective for new opened connections, that were created after the change was imposed. Currently opened connections wont be affected by the change.
Usage
The capability is configured using the same configuration options as the one required for using ProxySQL client SSL capabilities, which consists in a combination of:
-
The configuration variable:
-
mysql-have_ssl: Which is required to be set to true to enable SSL in client connections.
-
The certificate files:
-
${DATADIR_PATH}/proxysql-ca.pem: CA certificate to be used for client SSL connections.
-
${DATADIR_PATH}/proxysql-cert.pem: Server certificate used by ProxySQL for client SSL connections.
-
${DATADIR_PATH}/proxysql-key.pem: SSL key to be used by ProxySQL for client SSL connections.
This files can be replaced as always by self generated ones.
-
The new introduced Admin command: PROXYSQL RELOAD TLS.
-
This command forces the reload of the old certificates previously present in the files listed above, in favor of the new certificates contained in the replaced files. If the reload of the certificates fails due to an error, the query issued would fail to be executed, a message specifying the nature of the error would be found in ProxySQL error log, and the previous certificates would be preserved. Only in the case of a successful load of the new certificates the old ones would be replaced.
Full certificates renewal
Now it’s possible to use the previously described feature, in combination with already present ProxySQL SSL capabilities to perform a ** full certificate renewal at runtime **:
1. Renewal of backend certificates
For configuring the certificates for the backend connections, ProxySQL already offers the following configurations options:
-
mysql-ssl_p2s_ca: CA certificate to be supplied to backend connections.
-
mysql-ssl_p2s_cert: SSL certificate to be loaded by ProxySQL for backend server connections.
-
mysql-ssl_p2s_key: SSL key to be loaded by ProxySQL for backend connections.
-
mysql-ssl_p2s_cipher: Cipher to be used for backend connections.
Once this variables are pointing to the desired certificates and the desired Cipher to be used, it’s enough to perform the following command in ProxySQL Admin console: LOAD MYSQL VARIABLES TO RUNTIME.
After the previous command is executed, newer connections against ProxySQL
will be using the newer specified certificates paths and cipher. For checking that backend connections are indeed using SSL, the following command can be used, if the cipher has been updated, it should also reflect it’s new value:
mysql -h127.0.0.1 -P6033 -uroot -psecret -e 'SHOW SESSION STATUS LIKE "Ssl_cipher"'A renewal of the previously specified certificates that are being used by ProxySQL is possible via:
-
Modifying the previously specified variables to point to a new path holding the new certificate and issuing the Admin console command LOAD MYSQL VARIABLES TO RUNTIME. This operation is guaranteed to be atomic.
-
Replacing current certificates files pointed by previously mentioned variables with the new certificates. Since ProxySQL will be using the same paths to access to the new certificates, it’s very important to perform an atomic replacing operation otherwise errors during connection creation can occur.
2. Renewal of frontend certificates
For this we are going to make use of new ‘dynamic SSL’ ProxySQL capability. In order to replace the current certificates being used for client connections for ProxySQL it’s enough to:
-
Make sure SSL is enabled for client connections, if not, set mysql-have_ssl=true and then issue command: LOAD MYSQL VARIABLES TO RUNTIME.
-
Replace the previously mentioned certificates files, with the new certificates files:
-
${DATADIR_PATH}/proxysql-ca.pem
-
${DATADIR_PATH}/proxysql-cert.pem
-
${DATADIR_PATH}/proxysql-key.pem
- Issue the new command: PROXYSQL RELOAD TLS.
If all the operations were successful, to verify this, it’s important to remember to check ProxySQL error log for errors, the new certificates would be loaded, and will be used for all the new incoming connections.
Enhanced support for SPIFFE authentication
ProxySQL introduced SPIFFE support in version v2.1.0 and implementation has been enhanced in this latest ProxySQL release.
Feature description
Using this feature it’s possible to use ProxySQL in combination with SPIFFE authentitaction, this is done by means of:
-
User attribute spiffe_id: This user attribute should be configured with the name of the specific SPIFFE workload in which ProxySQL is going to be deployed. E.g.: ‘{“spiffe_id”: “spiffe://example.org/workload-proxysql”}’.
-
A client SSL connection supplying a certificate that can be verified against proxysql-cert.pem and which contains and X509v3 Subject Alternative Name SAN URI with the same ‘id’ as specified in the user attribute spiffe_id. E.g.: ‘X509v3 Subject Alternative Name: URI:spiffe://example.org/workload-proxysql’.
Important Note: ProxySQL doesn’t support mTLS support for SSL connections, it’s just in case a client connection supplies a certificate which holds a SAN URI identifier starting with ‘spiffe‘, like in the previously given example, that ProxySQL will perform the verification of the client certificate against proxysql-cert.pem.
Other introduced capabilities
New introduced SSL variables:
-
mysql-ssl_p2s_capath: Allows to set a path to a directory that contains trusted SSL certificate authority (CAPATH) certificate files in PEM format.
-
mysql-ssl_p2s_crl: Certificate revocation list.
-
mysql-ssl_p2s_crlpath: Certificate revocation list path.
With the inclusion of these variables ProxySQL now offers more flexibility on how to setup the CA certificates that shall be used for the SSL connection with mysql-ssl_p2s_capath, and also offers the possibility to impose a revocation list of the certificates with mysql-ssl_{crl,crlpath}.
Allow other certificates aside RSA:
ProxySQL now supports other key formats than RSA, for example EC keys. ¡Choose the encription that best suites your needs!
Final recap!
With all these new features ProxySQL now offers a richer SSL configuration experience which allows you to:
-
Reload all the certificates being used by ProxySQL with zero downtime!
-
Forget about user passwords or API keys with the enhanced SPIFFE support
-
Extra configuration capabilities for rejecting/accepting SSL certificates
-
Support for other key formats than RSA.
Happy secure ProxySQLing!